Cybersecurity for Connected Panel Systems
Securing networked panel assemblies against cyber threats.
Cybersecurity for Connected Panel Systems
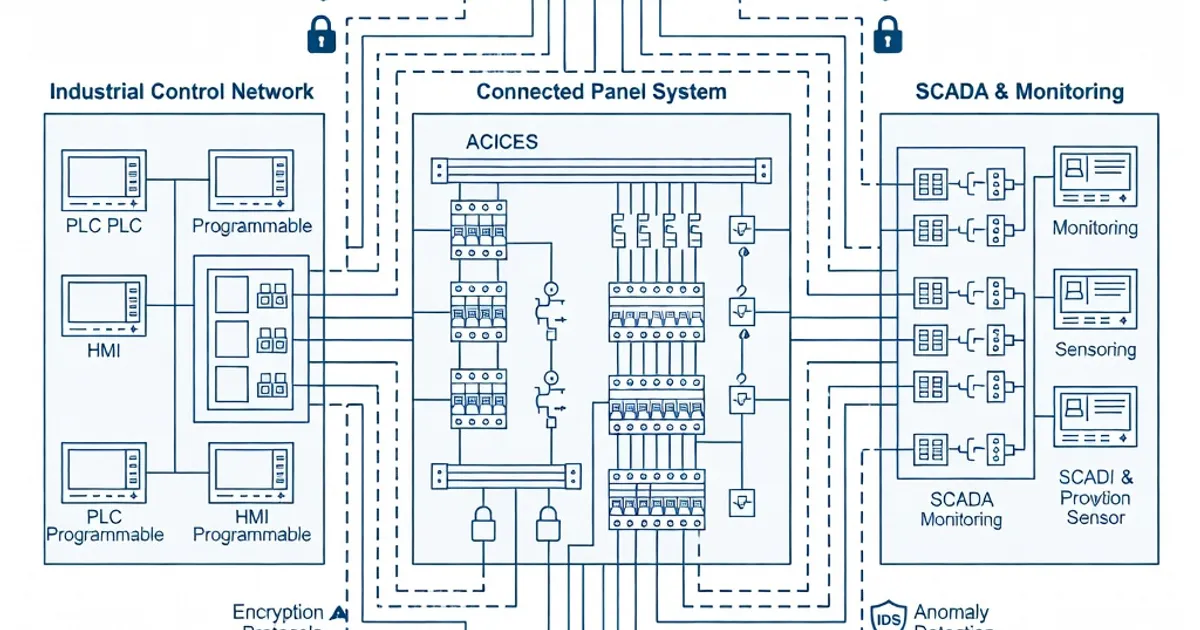
Modern low-voltage panel assemblies (LV switchgear and distribution panels) increasingly include networked monitoring, remote control, and IoT-enabled telemetry. While IEC 61439 (low-voltage switchgear and controlgear assemblies) governs the electrical, mechanical, thermal and safety performance of the physical assembly, it does not itself prescribe cybersecurity controls. For connected panel systems, cybersecurity is implemented by combining IEC 61439-compliant design and verification with industrial cybersecurity standards—primarily IEC 62443—and by applying engineering best practices (network zoning, secure updates, strong authentication, and logging). This article explains how IEC 61439 interacts with cybersecurity, summarizes the applicable standards, outlines specific controls and verification activities, and documents manufacturer and industry practices for secure connected panels.
Standards Landscape: What Governs Panels and What Governs Cybersecurity
IEC 61439 (Edition 3.0, 2020 for Part 1) provides the general rules and verification framework for LV assemblies. It focuses on electrical performance, mechanical integrity, environmental protection (IP per IEC 60529), clearances/creepage, temperature rise, dielectric properties and short‑circuit withstand, among other verifications [1][2][4][6][7]. IEC 61439 does not contain prescriptive cyber technical controls but does require that devices incorporated into an assembly meet their respective device standards and that internal circuits and mechanical arrangements do not impair device function—requirements that indirectly support secure operation of networked components (for example, prevention of heat or electromagnetic emissions that could affect communications) [2].
IEC 62443 is the accepted industrial automation and control systems (IACS) cybersecurity framework used to secure connected panels and their networks. IEC 62443 specifies security levels (SL 0–4), principles of defense-in-depth, requirements for zones and conduits, and functional cybersecurity requirements such as authentication, access control, logging, secure update mechanisms and network segmentation (industrial firewalls) [3]. Where IEC 61439 defines the verified integrity of the physical assembly, IEC 62443 defines how the panel’s electronic and software assets must be protected when exposed to OT/IT networks.
Other relevant standards include IEC 60947 for switching devices (ensuring devices behave as intended when incorporated into assemblies) and IEC 60529 for enclosure protection ratings (IP codes) which are essential for physical tamper-resistance complementary to cyber controls [2][6]. Energy and facility-level standards such as ISO 50001 can guide integration of telemetry and energy monitoring while maintaining secure data handling practices [3].
Key Standards and Their Roles
- IEC 61439 — Verification of LV assemblies: electrical, mechanical, thermal, internal wiring and device incorporation rules (Ed.3.0, 2020) [1][2][7].
- IEC 62443 — Industrial cybersecurity: zoning, conduits, security levels SL0–SL4, authentication, secure update, logging, and network segmentation (primary cybersecurity standard for panels) [3].
- IEC 60947 — Requirements for switching devices and protection equipment; assemblies must incorporate devices per their device standards without impairment [2].
- IEC 60529 — Degrees of protection provided by enclosures (IP codes) which support physical security and environmental protection [1][6].
How IEC 61439 Relates to Cybersecurity in Practice
IEC 61439 enforces a set of verifications and design constraints that have direct and indirect benefits for cybersecurity, even though the standard does not specify cyber controls. The relationship appears in two primary ways:
- Indirect technical compatibility: Clause 10 (incorporation of switching devices and components) requires that devices maintain their rated performance when assembled. This includes tolerance to heat, vibration and electromagnetic conditions created by the assembly—conditions that could otherwise impair secure communications or device behaviour. Ensuring device integrity reduces the likelihood of fault conditions that attackers could exploit [2].
- Internal wiring and segregation: Clause 11 (internal electrical circuits and connections) mandates secure wiring, segregation and mechanical protection of circuits. Correct internal layout reduces risk of cross-coupling, unintentional grounding or interference that may affect communications or cause false alarms in monitoring systems [2][6].
In short, IEC 61439 ensures the panel is physically and electrically fit for purpose; IEC 62443 ensures the panel’s electronic communication and control functions are protected when connected to a network.
IEC 61439 Verification Items and Cybersecurity Relevance
IEC 61439 defines a group of verifications (commonly referred to as the set of verification items for an assembly) that are applied by type-testing, routine testing, or comparison/assessment. These verifications include degree of protection (IP per IEC 60529), dielectric properties, temperature rise, short-circuit withstand, clearances/creepage distances, mechanical operation and verification of internal circuits. Each verification contributes to cyber resilience in specific ways (for example, an IP55 enclosure prevents physical tampering of network ports; robust internal wiring prevents intermittent communications faults) [1][2][4][6][7].
| Verification Property (IEC 61439) | Typical Test / Verification | Cybersecurity Relevance |
|---|---|---|
| Degree of protection (IEC 60529) | Ingress tests for solid/liq. protection (IP2X, IP54, IP55, etc.) | Physical barrier against tampering of network interfaces, protection of edge gateways and patch ports from environmental damage [1][6] |
| Dielectric and impulse withstand | High-voltage dielectric tests, impulse tests | Assures communication modules tolerate transients that might corrupt firmware or cause fail‑open states [1][2] |
| Temperature rise | Temperature profiling under rated current | Prevents thermal-related degradation of secure components (e.g., embedded gateways, secure elements) that could lead to failure modes exploitable by attackers [2] |
| Short-circuit withstand | High short-circuit current tests and protective device coordination | Ensures protection devices do not create unsafe fallback behaviour for network-connected devices during faults [1][2] |
| Internal circuits & segregation (Clauses 11) | Visual and functional verification of wiring, barriers and creepage/clearance | Prevents electrical interference and inadvertent connections that could compromise secure communications or cause corrupted telemetry [2][6] |
Cybersecurity Controls for Connected Panel Systems
To secure an IEC 61439-compliant connected panel, engineers must implement controls from IEC 62443 and accepted industry practices. The controls fall into network architecture, access control & authentication, device hardening & safe update, and monitoring & logging.
Network Architecture and Segmentation
- Design panels as part of a zoned OT network: isolate control panels in OT zones and use well-defined conduits controlled by industrial firewalls and data diodes where needed. Per IEC 62443, zone/conduit segmentation and defense-in-depth are primary strategies for limiting attacker movement and exposure [3].
- Use managed switches with VLANs and strict access control lists (ACLs) to restrict traffic to only required flows (Modbus/TCP, Profinet, OPC UA, etc.). This reduces the attack surface and limits broadcast domains that can propagate malformed traffic.
Access Control, Authentication and Authorization
- Require multi-factor authentication (MFA) for remote administrative access to HMIs, PLCs and gateway devices. IEC 62443 mandates authentication requirements aligned with security level objectives (SL 1–SL 4) [3].
- Implement role-based access control (RBAC) and least-privilege accounts. Use centralized identity stores (RADIUS, TACACS+) where possible to audit and manage credentials.
Secure Device Hardening and Firmware Updates
- Use secure boot, signed firmware images and integrity checks for gateways and edge devices. Ensure updates are delivered via encrypted channels and validated prior to installation in field devices, consistent with IEC 62443 requirements for secure update processes [3].
- Disable unnecessary services (unused ports, debug interfaces) on embedded gateways and energy meters to reduce attack vectors.
Monitoring, Logging and Incident Detection
- Collect audit logs, connection events, and system alerts centrally and retain logs per site policy. Configure alerts for failed logins, configuration changes and firmware update attempts.
- Consider anomaly detection: traffic baselining for panel telemetry helps detect exfiltration or command-and-control patterns early. Many vendors provide anomaly or signature-based detection integrated into their platforms [8].
Physical-Cyber Measures
- Match physical protection (IP rating, locked doors, tamper seals) to cyber controls. For example, an IP54/IP55 enclosure with locked access and intrusion detection makes physical tampering with network ports and USB interfaces more difficult [1][6].
- Add a tamper switch or lock sensor to trigger alerts when cabinet doors open; integrate those alerts with the SOC/ICS monitoring tools.
Verification and Testing: Combining IEC 61439 and IEC 62443
Verification for connected panels requires both the electrical/mechanical verifications of IEC 61439 and the functional/security verifications described by IEC 62443. Practically, project teams achieve compliance through a combined test and assessment plan:
- IEC 61439 verifications: execute type tests or apply comparison/assessment where applicable (e.g., dielectric, temperature rise, short-circuit, internal circuits, IP tests) to ensure reliable physical operation of the assembly [1][2][7].
- IEC 62443-based security verification: perform security requirement testing for access control, authentication, secure update, network segmentation and logging. Validate secure boot, signed firmware, TLS for protocols and hardened configurations on gateways and HMIs [3].
- Integration testing: test electrical stress conditions (temperature, mechanical vibration, EMI) while exercising communications to verify no functional degradation of secure communications—fulfilling the spirit of Clause 10/11 that device functions must not be impaired by the assembly [2][6].
Where full type testing is impractical, IEC 61439 allows a combination of type testing, routine testing and comparison/assessment to demonstrate conformity. For connected systems this can include documented evidence of cybersecurity design and verification aligned with IEC 62443, combined with IEC 61439 electrical/physical verification reports [1][2][4].
Manufacturer Practices and Product Examples
Major panel manufacturers produce IEC 61439-compliant panels with embedded cybersecurity features that align to IEC 62443. These examples illustrate how vendors package electrical and cyber compliance together:
- Siemens: Offers LV switchgear and panel solutions (e.g., SIVACON / Sentron families) that integrate secure communication modules, gateway devices and support for industrial protocols with security extensions (such as PROFINET security and Modbus/TCP Secure). Manufacturers document secure configuration guidance and hardening measures for panels [8].
- ABB: ABB Ability-enabled switchgear and connected panels incorporate edge gateways and platform services with secure update processes, MFA for remote access, and encrypted telemetry transport as part of the ABB Ability cybersecurity architecture [5].
- Schneider Electric: EcoStruxure Power and Okken/PrismaSe product lines include secure gateways, integrated logging and optional managed cyber services. Schneider documents IEC 61439 guidance for panel builders and publishes cybersecurity service offerings aligned to IEC 62443 SL2/SL3 [8].
- Eaton and Rittal: Provide panel products with embedded telemetry and gateway hardware offering VPN, secure boot and configuration hardening options; Rittal supplies enclosure and busbar systems with IoT gateway integration designed for secure operation in IEC 61439 assemblies.
Product documentation and vendor application notes detail concrete configurations, such as recommended firewall rules, required TLS versions, support for signed firmware and device lifecycle guidance. Project teams should require these documents and ask for evidence of vendor adherence to IEC 62443 where critical.
Best Practices for Engineers and Panel Builders
Below are practical guidelines to apply during design, assembly and commissioning of connected panels:
- Start with a joint requirement set: capture both IEC 61439 electrical/physical requirements and IEC 62443 security requirements early in specification documents. Define desired IEC 62443 security level (e.g., SL1 or SL2) for the panel and surrounding network.
- Design for segregation: physically separate power/control wiring from communications wiring; mount gateways and switches in locked compartments and provide secure conduit access for network cabling.
- Hardening checklist
Related Panel Types
Frequently Asked Questions
Request a Quote
Tell us about your panel requirements and our engineering team will get back to you within 24 hours.
Email Us
[email protected]Call Us
+90 232 332 22 78